Single Sign-On
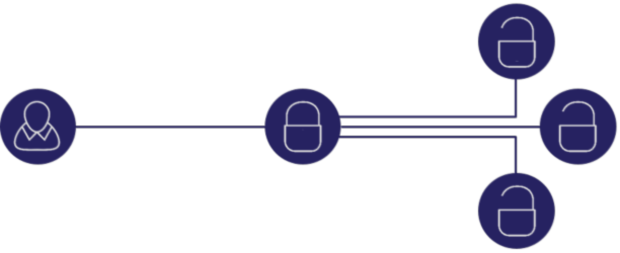
Enterprise Single Sign-On (SSO) and Session Sharing across multiple domains
With an increasing number of systems and applications follows an increasing number of username and passwords. That is why Ceptor offers enterprise SSO and session sharing across your entire application portfolio. SSO enhance your infrastructure with simplicity and improves user experience as the user is relieved of remembering numerous login details.
Session sharing enables SSO across applications by only sharing the session key – any updates are immediately available to all applications, and usage of the shared session enables high security across all your applications by hiding individual server cookies within the session. Read more about Ceptor SSO
All Users
Build to support all your users: customers, employees, partners and even your devices.
All Applications
Integrates with your enterprise applications across any platform both on-premise and in cloud.
All Devices
Enable access for all devices:
laptop, tablet, smartphone and IoT devices.
What is Ceptor?
Secure IT Infrastructure
Ceptor is a Secure IT Infrastructure solution that protects your applications behind our sophisticated Reverse Proxy. Ceptor also provides single sign-on and security for all your enterprise systems. Read more about Ceptor Gateway
Configurable
Configured to support any size of installations - both on-premise, cloud and hybrid - and can easily be scale if your demands change. Proven to support the largest enterprise installations with hundreds of applications and hundreds of thousands of concurrent users. Currently, we protect some of the largest websites for some of the largest Danish enterprises. See our Clients
Developed by Experts
Designed and developed by IT security experts together with the sharpest operations specialists. Our goal is to create the strongest security infrastructure possible with a minimum of performance overhead, whilst being simple to operate in even in the most complex environments. Read more about Us
Complexity, Not a Problem
Even if you have the most complex infrastructure and security needs are, Ceptor can handle that. Created to be extremely flexible, Ceptor is far more than just another security product; it is a secure IT infrastructure supporting very complex setups, multiple platforms and extreme large-scale application setups. Read more about Platforms
Performance Driven
Engineered from the ground up with high performance in mind without compromising security. Easily allows thousands of concurrent requests and is proven in complex high availability setups. You can from a single centrally managed installation run multiple separate clusters, thus separating e.g. intranet and internet sessions from each other if required for security policy or legal reasons.
Multiple Configurations
Ensure a comprehensive security setup, whilst offering you the freedom to choose amongst Application Server Plugins and Authentication Plugins that suit your business needs.
We know that it is important to stay on top of trends, especially within IT security. That is why we have made it easy for our customers to adapt to both external and internal influence. We support your existing setup and the setup of our future needs. It does not matter what your needs are – could be Single Sign-On (SSO), Multi-Factor Authentication, Biometric Access – we will make it work!
What will Ceptor cost me?
Design your desired configuration to enable us to quote your license